Question 1 of 20
When an entity has the primary key of another entity as an attribute, this creates:
This A Level Computer Science Quiz 2020 Part 3 quiz contains 20 multiple choice questions designed to help you revise and test your A level Computer Science Quizzes knowledge. Select an answer for each question and click “Submit Answer” to see instant feedback. Take your time and try to score as high as possible!
The study of computers and their architecture that deals with directory of computation or the design of computers. The world is what it is today in terms of technological advancement due to the knowledge acquired from computers and its application.
In paper one of the Advance level GCE examinations, students always face a lot of difficulties because of the similarity among answers and always have a myth that it is almost impossible to have a good grade from this section of the examination. To help students change this mindset and prepare them for any computer science examination.
The quiz is made of 20 questions only. Questions are based on the topics “Data communications and networking, data algorithms and structure etc.
To have more resourceful materials such as this quiz, you can visit our website.
Good luck!!!
Question 1 of 20
When an entity has the primary key of another entity as an attribute, this creates:
Question 2 of 20
Which of the following is not the required condition for binary search algorithm?
Question 3 of 20
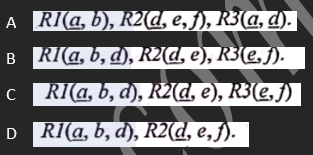
In the database relation R (a, b, d, e, f) attribute b and d are dependent only on a; e only on d; and f only on d. which of these sets of relations is equivalent to R in third normal form (3NF), if key attributes are underlined?
Question 4 of 20
When data goes through a network, data privacy is available when:
Question 5 of 20
Only authorised people can access and modify information through a network
Question 6 of 20
How many distinct memory addresses can a processor access if its machine word has 8 bytes?
Question 7 of 20
The design strategy that identifies subtasks based on the operations carried out in them to provide a service or feature is known as:
Question 8 of 20
A binary tree whose every node has either zero or two children is called:
Question 9 of 20
The post order transversal of a binary tree is DEBFCA. Find out the preorder transversal.
Question 10 of 20
Which of the following sorting algorithms is of divide-and-conquer type?
Question 11 of 20
Program Readability is typically understood to be:
Question 12 of 20
It is used how values change in memory locations, without program instructions, or altering memory locations; during debugging
Question 13 of 20
Some programs will always guarantee an answer if there is one, but may run for ever if there is none. Such problems are:
Question 14 of 20
Algorithms or problems they solve are sometimes described as hard or intractable. This is often a measure of:
Question 15 of 20
Prototyping is a technique that:
Question 16 of 20
The space factor when determining the efficiency of algorithm is measured by counting the:
Question 17 of 20
To solve a certain problem, some of its procedures are executed on distinct machines, possibly across the world. We designed a(an):
Question 18 of 20
The following are in distinct classes of declarative languages:
Question 19 of 20
Programming language (PL) functions are designed to return a value; the values returned by PL functions are often passed in other function or procedures:
Question 20 of 20
We examine a program, executing and checking its instructions, so as to establish that it behaves as expected. We are doing:
With the new age of technology, we must have come across so many definition...
The world of technology is quickly changing our life. The world of computer...
Computer science is a vast field encompassing various aspects related to co...
Computer science encompasses a very wide range of fields, and new ones cont...